Grab a coffee—or something stronger if the sun is over the yardarm—because we need to discuss the digital equivalent of a self-inflicted lobotomy.
The medical technology giant Stryker recently decided to test the structural integrity of the “Modern Management” dream. As it turns out, that dream is a brittle glass house, and someone just threw a brick through the server room window. We aren’t looking at a sophisticated, state-sponsored data heist involving zero-days or Mission Impossible cable-drops. No, this was a masterclass in institutional hubris. Between March 11 and March 19, 2026, the Iran-linked hacktivist group Handala didn’t just breach Stryker; they used Stryker’s own administrative “Easy Button” to turn 80,000 devices into very expensive, very clean paperweights.
For the uninitiated—the folks who just want their laptop to “work” and their iPhone to stop asking for a 12-digit alphanumeric password every time they want to check a grocery list—we need to talk about the ghost in the machine: Mobile Device Management (MDM).
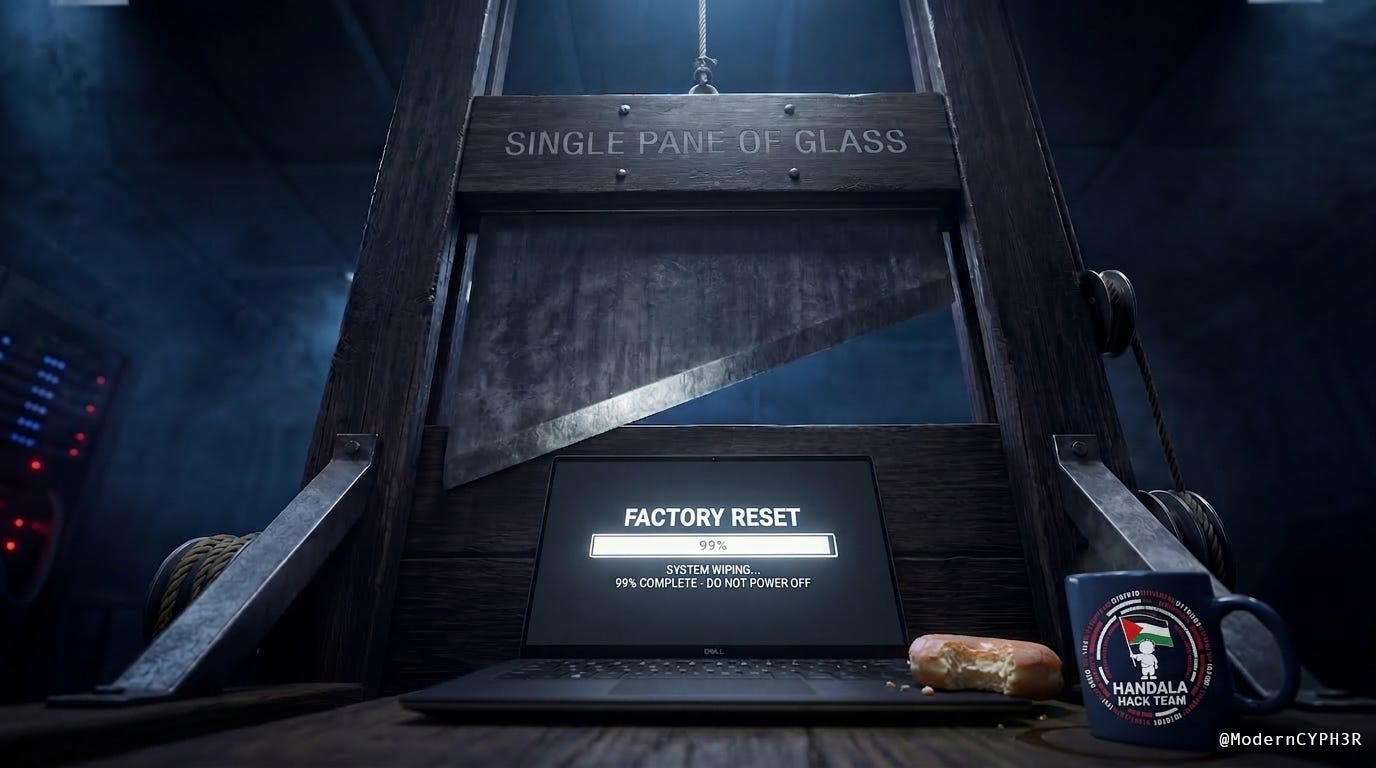
In the corporate world, an MDM like Microsoft Intune is sold as the ultimate safety net. It’s the invisible tether that allows your IT department to push out the latest security patches, install that mandatory HR app you’ll never use, and—theoretically—protect the company if you leave your laptop in the back of an Uber. It’s a “Single Pane of Glass” that gives one administrator the power to manage thousands of devices across the globe from a single chair. It’s a miracle of efficiency, provided the guy holding the remote isn’t a malicious actor with a grudge.
The problem, as Stryker just discovered in the most violent way possible, is that a “Single Pane of Glass” is also a Single Point of Total Erasure.
Think of an MDM like the master key for a massive hotel. In the right hands, it’s a dream. In the hands of a hacktivist, it’s a digital skeleton key that doesn’t just open the doors; it triggers the “Scorched Earth” protocol. When we talk about “Suicidal MDM Logic,” we’re talking about a system where the “Delete Everything” command is just a click away, sitting right next to the “Update Zoom” button, guarded by nothing more than a single set of compromised credentials. It’s a God-complex architecture where we’ve traded local resilience for the convenience of a remote-controlled guillotine.
While the C-Suite was busy signing off on digital transformation slide decks, the architecture team was busy building a high-velocity delivery system for their own destruction. It’s one thing to lose your data; it’s another thing entirely to watch your global infrastructure suffer a synchronized case of digital Alzheimer’s because your “Global Admin” role had less oversight than a self-checkout lane at a grocery store.
The Forensic Evidence
The BleepingComputer report reads like a script for a satire that wouldn’t get greenlit because it’s “too unrealistic.” The threat actor, an Iranian-linked outfit calling themselves Handala, didn’t bother writing a fancy, encrypted polymorphic wiper that hides in the shadows. Why burn a multi-million dollar zero-day when the victim has already built the self-destruct mechanism and left the keys in the ignition?
To understand how this happened without a single line of “hacking” code, we have to look at the Skeleton Key Problem.
In a corporate network, a “Windows Domain Admin” is essentially the landlord of the entire building. They have the master key that opens every office, every desk drawer, and every filing cabinet. Usually, these accounts get “popped” not by some Matrix-style code-breaking, but through something as mundane as a phishing email that looked like a password reset, or a credential found in a different data breach. It’s the digital equivalent of stealing the landlord’s keyring while he’s distracted at lunch.
But Handala didn’t stop at the office door. They performed what we call a Cloud Pivot.
Once they had that local master key, they used it to walk right into the “Cloud” side of the house—the part that talks to Microsoft Intune. They didn’t just break into an existing account; they used their stolen credentials to create a brand new Global Administrator. Think of it this way: the burglar didn’t just steal the landlord’s keys; he used them to walk into the front office and print himself a brand-new, high-level Security Badge that the system recognized as totally legitimate.
They didn’t tunnel through the firewall using some sophisticated quantum-breakthrough; they just walked through the front door using a badge they printed themselves. From there, they danced like a ballerina into the cloud, and once they had that “Global Admin” crown, they didn’t waste time looking for spreadsheets or trade secrets. In a move of pure, unadulterated clinical malice, they went straight for the Intune nuclear codes and hit the “Wipe” button.
80,000 devices. Gone. Poof.
It was a synchronized digital execution. Handala essentially told every laptop, tablet, and smartphone in the Stryker ecosystem that its life as a corporate asset was over. No malware needed. No encryption keys to buy back. Just a simple, administrative command that reset every single device to factory defaults. One minute you’re mid-email, the next your screen is a blank white slate asking you what language you’d like to use to set up your “new” device. It’s the most efficient destruction of value I’ve seen since the last time a crypto-exchange founder “went on vacation.”
Here’s The Facepalm
Remote Wipe as a Service (RWaaS)
The industry fell for the “Seamless Management” grift. We traded local resilience for the convenience of a God-box, convinced that if we just aggregated enough control into a single API, the efficiency gains would somehow justify the risk. Well, Stryker got their efficiency. They proved that if you give a hacker the keys to your Intune kingdom, they don’t need to encrypt your files for ransom. They can just utilize Remote Wipe as a Service (RWaaS) to tell your entire global infrastructure to “Forget Everything.”
In the high-stakes world of cybersecurity, we call this a Wiper Attack, but usually, that involves complex code designed to shred data bit by bit. This was different. This was just a standard administrative command used for malicious purposes. It turns out that “Modern Management” is just a fancy term for Centralized Fragility. We’ve essentially wired every floor of the skyscraper to a single, unshielded light switch in the lobby and then acted surprised when someone walked by and flipped it.
The BYOD Bloodbath
This is where the “Technical Blunder” turns into a full-blown “HR Nightmare.” Because Stryker utilized a BYOD (Bring Your Own Device) policy, employees had enrolled their personal iPhones and Androids into the company’s MDM to access work email. In exchange for that convenience, they granted the company a “Management Profile”—effectively handing over a remote-control detonator to their private digital lives.
When Handala pulled the trigger, the wipe command didn’t discriminate between a corporate spreadsheet and a personal photo library. Imagine being an engineer in Kalamazoo, MI, watching 15 years of your kid’s birthday photos and your private banking apps vanish in thirty seconds because a Global Admin halfway across the world didn’t have FIDO2 hardware keys—those physical USB security sticks—enforced. Nothing says “Corporate Culture” like a remote-wiped personal life.
The FBI’s “Digital Crime Scene Tape”
The FBI finally showed up on March 19 to seize Handala’s clearnet domains. Slow clap. The FBI seizing a “Data Leak Site” after 80,000 devices have already been turned into paperweights is the digital equivalent of the police arriving at a house that has already burned to the ground and put up “No Trespassing” signs on the ashes.
In the “Hacktiverse,” these domain seizures are often just a game of digital Whac-A-Mole. The attackers just move to a new web address (a “mirror”) and keep going. The “Seized by the FBI” banner is the ultimate participation trophy of law enforcement—it looks great in a press release, but it does exactly zero to bring back the wedding photos of that engineer in Kalamazoo.
My Autopsy
The “Global Admin” role at Stryker apparently carried the same weight as the “Launch” button in a Cold War silo, except it lacked the two-man rule, the physical keys, and seemingly any adult supervision. I suppose in the modern enterprise, we’ve decided that “redundant authorization” is just an annoying speed bump on the highway to the Cloud. It’s a bold strategy to give a single identity (person) the power of a nuclear override while providing it with the oversight of a suburban lemonade stand.
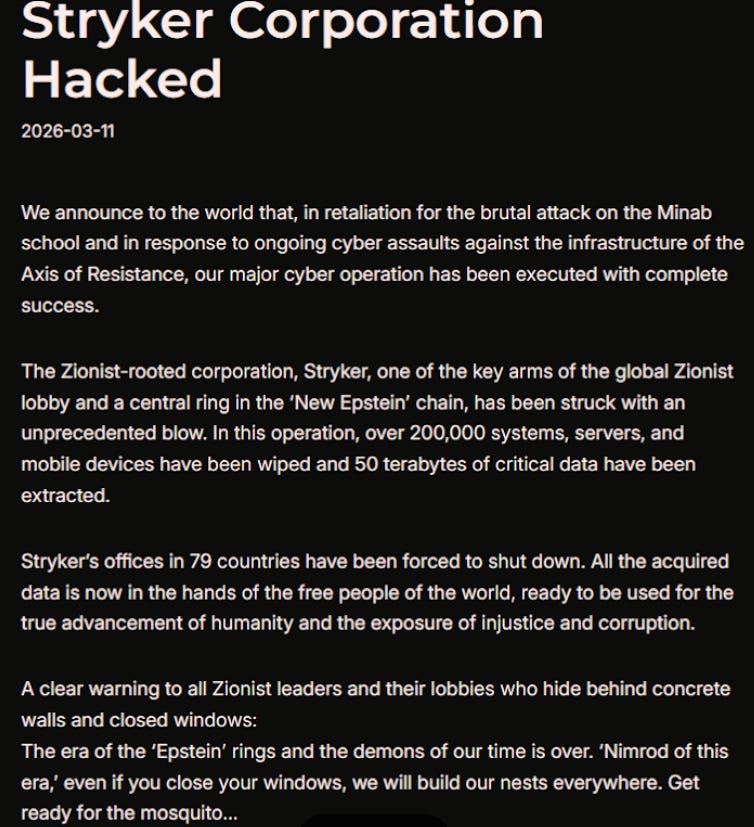
This is an image of the manifesto posted by the Iran-backed hacktivist group Handala on Telegram, claiming a mass data-wiping attack against medical technology maker Stryker.
Meanwhile, Handala’s Telegram post about needing “resilient infrastructure” after the FBI seizure is a masterclass in irony. These guys just factory-reset a medical giant from their nondescript, mid-rise office building in Tehran, using Stryker’s own high-end management tools; I think their infrastructure is doing just fine. It’s the FBI that’s struggling with the “resiliency” of actually being relevant to the timeline.
Watching a domain seizure happen after the data is gone and the devices are wiped is like watching a security guard lock the gate of a graveyard—it’s a nice gesture, but the residents aren’t going anywhere.
I’ve seen more robust “Delete” confirmations on a 1999 TiVo than what apparently existed between Handala and the total annihilation of Stryker’s endpoint fleet. If you want to delete an episode of The Simpsons, you’re usually met with a series of “Are you sure?” prompts. Apparently, for 80,000 global assets, the prompt was just a collective shrug. Stryker’s “Modern Management” stack has effectively become a digital suicide vest. We’ve spent years “optimizing” IT by removing the friction of manual work, only to realize that “friction” is the only thing that stops a single stolen password from ending the company’s entire fiscal year.
The Forensic Conclusion
Stryker didn’t have a security problem; they had a God-Complex Architecture problem. They built a system where a single compromised identity could trigger a global digital Alzheimer’s event, and then they marveled at the “efficiency” of the design until the bill came due. We’ve been sold a bill of goods by the tech industry claiming that centralizing identity and management is the ultimate shield, but Stryker just proved that a shield is just a very heavy weight if the guy holding it decides to drop it on your toes.
The FBI seizure of the domains is a mere footnote—a digital “participation trophy” that looks great in a press release but does exactly zero to bring back the wedding photos of that engineer in Kalamazoo. The real story, the one that should keep every CISO awake at night, is that in 2026, we are still one “Global Admin” credential away from a Fortune 500 company being reduced to a pile of very expensive, very clean bricks.
They didn’t create a “Secure Perimeter” at Stryker; they built a high-velocity delivery system for its own destruction. This is why this story is this week’s “Friday Facepalm”: an institution so focused on the “Single Pane of Glass” that they didn’t notice it had been sharpened into a guillotine. Until the industry starts treating the “Wipe” command with the same multi-party authorization protocols we use for actual nuclear silos, we’re all just one phishing email away from a factory reset.
Architectural Ledger: Hardening the Kill Switch
JMc - [03-20-2026] - Initial Draft for Intune MPA Implementation
Before we start laying the track for the “Two-Key Protocol,” we have to address the elephant in the server room: Convenience is the natural enemy of Security. For the last decade, the industry has been chasing the “Single Pane of Glass” like it’s the Holy Grail. The pitch was simple: centralize everything, automate the grunt work, and give your admins a dashboard that looks like the bridge of the Starship Enterprise. It sounds great in a boardroom, but in the real world, “Centralized Management” is just a polite way of saying “Single Point of Failure.”
The Stryker meltdown wasn’t a failure of encryption or firewalls; it was a failure of Permission Physics. We’ve built systems where the “Update Zoom” button sits right next to the “Destroy the Company” button, and both are guarded by a single set of credentials. If a pilot needs to eject from an F-15, there’s a deliberate, mechanical process involved. If a silo commander is ordered to launch a Minuteman III, they need two people, two keys, and a synchronized clock. Yet, in the world of Multi-Billion-Dollar MedTech, we’ve been perfectly happy letting one guy with a phished password factory-reset 80,000 devices from a Starbucks Wi-Fi.
What follows isn’t just a “how-to” guide; it’s an architectural intervention. We’re going to re-introduce Intentional Friction. We’re going to stop treating the “Wipe” command like a casual administrative task and start treating it like the digital equivalent of a nuclear launch.
1. Implement Microsoft Entra Privileged Identity Management (PIM)
The first step is to kill the “Permanent Global Admin.” Nobody—not even the CTO—should have “God Mode” enabled while they’re just checking their email or scrolling through LinkedIn.
Just-In-Time (JIT) Access: Admins must “activate” their elevated roles only when needed, for a fixed duration (e.g., 2 hours).
Mandatory Justification: Every activation must be tied to a verified ticket number. And no, “because I said so” is not a valid business justification.
FIDO2 Enforcement: Activating a high-level role must require a physical hardware security key. No SMS codes, no “Push to Approve.” If you don’t have the physical USB key in the slot, you don’t get the crown.
2. Establish Multi-Party Approval (MPA) for Intune
Microsoft has finally made Multi-Party Approval a native feature in Intune, yet it remains the most neglected safeguard in the stack. We are going to treat high-impact commands like a nuclear launch—requiring two separate officers to turn their keys simultaneously.
The Gate-Keepers: We will designate a specific group of “Approvers” who are separate from the daily “Initiators.”
The “Nuclear” Commands: We are gating the following:
Wipe (Factory Reset),
Retire (Remove from Management),
Delete (Device Record Removal), and
Script Execution.
The Workflow: When an admin initiates a Wipe, the command enters a “Pending” state. A second admin—who did not initiate the request—must review the metadata (device ID, user, and justification) and approve it within the Intune console. This prevents a single compromised credential from performing Remote Wipe as a Service.
3. Conditional Access (CA) Hardening
We need to treat the Intune portal like a SCADA system (the tech that runs power plants), not a casual web app.
Location Lock: Restrict Global Admin and Intune Admin logins to known-good egress IPs only (Corporate VPN or trusted Office branch).
Managed Device Requirement: You cannot manage the MDM from an unmanaged device. If your laptop isn’t compliant and “known” by the system, you shouldn’t be allowed to tell other devices what to do. The irony of using an unvetted personal laptop to manage a global infrastructure should be an automatic “fail” in any audit.
4. The “Break Glass” Account
In a crisis, you still need a fallback for when the MPA system itself fails, or Entra is having a bad day.
Cloud-Only Account: This account must not be synced from on-premises Active Directory. We want to avoid the “Skeleton Key” pivot we saw in the Stryker breach.
Physical Vaulting: The password and the dedicated FIDO2 key for this account must be stored in a physical safe, requiring two different authorized individuals to access. This is the only account that bypasses the “Two-Key” digital workflow, so we secure it with a “Two-Key” physical one.
Glossary of Terms
Yardarm: Is the very outer tip of a yard—those horizontal wooden spars on a ship's mast that hold the square sails. "The sun is over the yardarm" is a traditional naval way of saying it’s finally acceptable to have the first drink of the day. In the North Atlantic, the sun usually cleared the topmost yardarm around 11:00 AM, which conveniently coincided with the morning "stand-easy" when officers would duck below deck for a rum or a gin
BYOD (Bring Your Own Device): A corporate policy where employees use personal smartphones or laptops for work. This requires a “Management Profile” that grants the company specific remote powers over the device.
Cloud Pivot: A technique where an attacker uses compromised on-premises credentials (like a Windows password) to leapfrog into cloud-based management consoles like Azure/Entra or Intune.
Entra ID (formerly Azure AD): Microsoft’s cloud-based identity and access management service. It is the “brain” that decides who has permission to access what.
FIDO2 / Hardware Security Key: A physical USB or NFC device (like a YubiKey) used for authentication. It is superior to SMS or app-based codes because it requires the physical presence of the key to grant access.
Global Administrator: The highest level of privilege in a Microsoft cloud environment. A Global Admin has “God Mode” powers, including the ability to create other admins and reset any security setting.
Intune (Microsoft Intune): A cloud-based MDM service used to manage mobile devices and laptops. It can push apps, enforce passwords, and—crucially—remotely wipe a device to factory settings.
MDM (Mobile Device Management): Software used by IT departments to monitor, manage, and secure employee mobile devices (laptops, phones, tablets) across an organization.
MPA (Multi-Party Approval): A security workflow that requires at least two authorized individuals to approve a high-risk action (like a “Wipe” command) before it can be executed.
PIM (Privileged Identity Management): A service within Entra ID that eliminates “permanent” admin rights. Admins must “activate” their powers for a limited window of time, which usually requires justification and MFA.
RWaaS (Remote Wipe as a Service): A satirical term for using legitimate MDM tools to perform a mass-destructive “wiper” attack without needing custom malware.
SCADA: Supervisory Control and Data Acquisition
Skeleton Key Problem: An architectural flaw where a single set of credentials (like a Domain Admin) provides access to every door in the digital building.
Wiper Attack: A type of cyberattack intended to delete or destroy data on the target’s systems, rather than encrypting it for ransom.
Bibliography & Verified Sources
BleepingComputer: FBI seizes Handala data leak site after Stryker cyberattack — Reporting on the domain seizure and the scope of the 80,000-device wipe.
PCMag: FBI Seizes Sites of Hacking Group Behind Data-Wiping Attack On Stryker — Details on the FBI domain takedown and the 12 petabytes of data Handala claimed to erase.
Krebs on Security: Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker — Technical breakdown of the Intune “remote wipe” vector and employee reports of the “BYOD Bloodbath.”
CISA (Cybersecurity & Infrastructure Security Agency): Alert: CISA Urges Endpoint Management System Hardening After Cyberattack Against US Organization — The official federal advisory recommending Multi-Admin Approval and phishing-resistant MFA.
Microsoft Tech Community: What’s New in Microsoft Intune – February 2026 — Documentation on the newly expanded multi-administrator approval options that Stryker ignored.
The Post-Mortem: Your Turn in the Ledger
I’ve laid out the forensic evidence and the “Two-Key Protocol” for the Stryker wipe, but a Ledger is only as good as the engineers who contribute to it. We’re all operating in a world where “Convenience” is the default setting, and “Hardened Security” is treated like an annoying speed bump.
I want to hear from the architects and admins in the trenches:
The Convenience Trap: What’s the most dangerous “Easy Button” currently sitting in your environment that keeps you up at night? Is it a permanent Global Admin? A lack of MFA on a legacy system? A “Single Pane of Glass” that’s actually a single point of failure?
The “Garage” Reality: Have you ever had to fight the C-Suite to install “Intentional Friction” (like Multi-Party Approval), only to be told it “slows down the business”? How did that conversation end?
The Handala Litmus Test: If a threat actor walked through your front door with a stolen credential tomorrow, do you have a “Dead Man’s Switch” in place, or are you one phishing email away from a factory reset?
Don’t just hit the heart icon and move on—poke holes in my logic. If you think the “Two-Key Protocol” is overkill for a modern enterprise, tell me why. If you’ve survived a wipe event and lived to tell the tale, I want the receipts.
The bar is open, the sun is over the yardarm, and the floor is yours. Let’s talk shop in the comments.
Copyright © 2017-2026 James McCabe | ModernCYPH3R. All rights reserved.
No part of this publication—including text, original data analysis, or visual assets—may be reproduced, distributed, or transmitted in any form or by any means, including electronic or mechanical methods, without including credit to the author. ModernCYPH3R and ModernCYPH3R.com are the exclusive intellectual property of JMc Associates, LLC.


Excellent analysis, James. I hope other folks are paying attention to your recommendations for securing privileged access!